Security Crash Course 2025
Unlock expert Google Cloud security insights in a series of 1-hour webinars
Now on-demand!

Level up your Google Cloud security skills in 6 weeks.
In the face of increasingly sophisticated cloud threats, continuous skill enhancement is paramount. SADA and Google Cloud are offering a no-cost, six-week intensive bootcamp specifically designed for cloud security engineers and IT professionals looking to excel in advanced security strategies on Google Cloud.
Who should attend?
Technical personnel looking to build their cloud security knowledge and skills. Anyone interested in learning more about Security.
Learn from industry leaders
Each lesson is hosted by leading experts from Google Cloud and SADA. You’ll get hands-on training from the world’s foremost authorities on Google’s Cloud Security.
Get access to valuable resources
Supplement your learning with new resources provided weekly. You’ll enjoy access to labs, videos, documentation, and tutorials.
Watch on-demand
Course Overview
Each session provides hands-on training and guidance by leading SADA and Google Cloud engineers. By the end of this six-week course, you’ll gain the practical knowledge to proactively secure and optimize your cloud environments.
AGENDA
Speakers
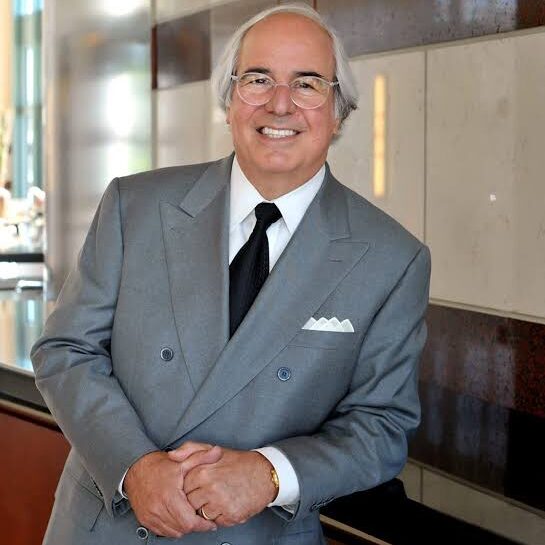
Frank Abagnale
John Giglio

Rocky Giglio

Hayden Holland

Likhita Singla

Jonathan Moisan

Tarun Sharma

Marco Genovese

Robert Teller

John Bacon

Jake Luna
Solve not just for today but for what's next.
We'll help you harness the immense power of Google Cloud to solve your business challenge and transform the way you work.








